Your suppliers are your biggest blind spot.
Right now, the supply chain is a massive problem for cybersecurity and business continuity. 63% of breaches start through a third party. Not your network - your vendor's network.
Asking "do you have good security?" on a vendor form doesn't cut it anymore.
The Third-Party Problem
Here's what actually happens: You secure your own systems. You train your staff. You implement controls. But then a vendor with access to your customer data gets breached, and suddenly your carefully constructed security posture means nothing.
The 2013 Target breach? Started with an HVAC contractor. The 2020 SolarWinds attack? Compromised thousands of organizations through a single software vendor. The 2021 Kaseya ransomware? Hit 1,500 businesses through one managed service provider.
Your security is only as strong as your weakest supplier.
Why Traditional Vendor Assessments Don't Work
Most organizations handle third-party risk with annual questionnaires. Vendors fill out a spreadsheet, someone reviews it, and it gets filed away until next year.
This approach has three fundamental problems:
- It's a point-in-time snapshot - A vendor's security posture in January tells you nothing about their posture in November
- Self-reporting is unreliable - Vendors have every incentive to present themselves favorably, and most don't have security expertise to accurately assess themselves
- There's no standardization - Every organization uses different questionnaires, making it impossible to compare vendors or track improvement
And let's be honest: most vendor questionnaires sit in someone's inbox for weeks before getting filled out at the last minute by whoever is available, regardless of whether they actually know the answers.
What Regulators and Insurers Now Require
The regulatory landscape is changing fast. SEC, DORA, NIS2 - they all now require third-party risk management. Not as a nice-to-have, but as a fundamental compliance requirement.
Your cyber insurance? They're asking about vendor security during underwriting. If you can't demonstrate systematic third-party risk assessment, expect higher premiums or coverage limitations.
And if your supplier gets breached and takes you down with them? That's on you. "We didn't know" isn't a defense anymore.
What We Just Launched
RateYourCyber now does continuous third-party risk assessments. Here's how it works:
Flexible Assessment Depth
Not every vendor needs the same level of scrutiny. A supplier with access to your core customer database requires more thorough assessment than a vendor providing office supplies.
We offer three questionnaire options:
- Simple (20 questions) - Quick assessment for low-risk vendors, takes 15-20 minutes
- Sophisticated (80+ questions) - Comprehensive evaluation for medium-risk suppliers
- Comprehensive (150+ questions) - Deep dive for critical vendors with access to sensitive data or systems
You choose the depth based on the vendor's access level, data sensitivity, and business criticality.
AI-Assisted Completion
Vendors don't need security expertise to complete assessments. Our AI assistant helps them understand questions and provides context, dramatically reducing completion time and improving accuracy.
Instead of vendors struggling with technical jargon, they get plain-English explanations and examples. This means assessments actually get completed rather than abandoned halfway through.
Automatic Risk Scoring
Once a vendor completes an assessment, they're automatically scored against industry benchmarks. You immediately see:
- Overall security maturity score
- Domain-by-domain breakdown (access control, incident response, data protection, etc.)
- How they compare to industry peers
- Specific risk flags requiring attention
No manual analysis required. No waiting for security teams to review responses. Instant, actionable risk visibility.
Week-by-Week Remediation Roadmaps
When gaps are identified, vendors don't just get a list of problems. They get a structured remediation roadmap showing exactly what to fix, in what order, with time estimates.
This transforms vendor assessments from compliance exercises into improvement programs. Vendors can track their progress and you can monitor remediation in real-time.
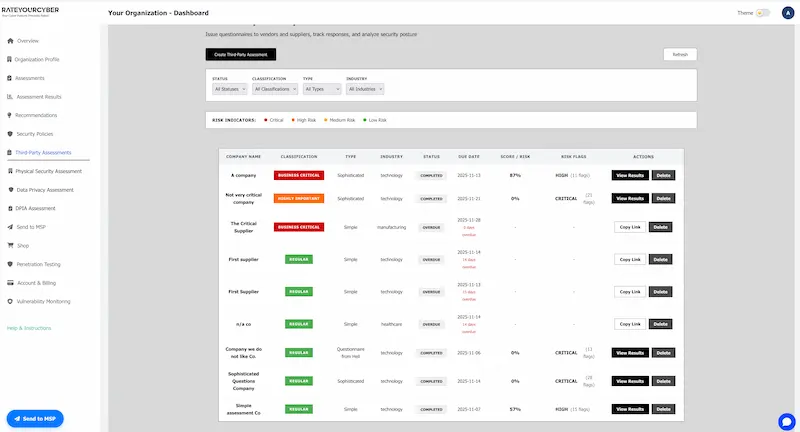
Real-Time Dashboards
Your dashboard shows which vendors represent your biggest risks at a glance. Sort by risk level, see trends over time, and identify vendors that need immediate attention.
When a critical vulnerability is disclosed that affects multiple vendors, you instantly know which suppliers are impacted and what their remediation timeline looks like.
Contract Clauses Based on Actual Gaps
Generic vendor security clauses don't address specific risks. When you identify gaps in a vendor's security posture, the platform generates tailored contract language to address those exact issues.
Need the vendor to implement multi-factor authentication within 90 days? The system generates appropriate contractual language with clear timelines and remediation requirements.
Plain English. Zero Jargon. Board-Ready.
All results are presented in language that makes sense to anyone - from technical teams to board members. No security degree required to understand which vendors pose the biggest risk.
Why This Matters Now
Regulators are coming. SEC, DORA, NIS2 all require third-party risk management. Your cyber insurance? They're asking about vendor security now too. And if your supplier gets breached and takes you down with them? That's on you.
The old way of handling vendor risk - annual spreadsheets filed away and forgotten - exposes you to regulatory penalties, insurance premium increases, and actual breaches.
The Difference
Old way: Annual spreadsheet. Filed away. Breach happens. "How did we miss this?"
New way: Continuous monitoring. Clear risk visibility. Fix issues before they become breaches.
No security team required. No consultant fees. Fraction of the enterprise tool price.
Who Should Use This
Third-party risk assessments are essential for:
- Organizations with complex supply chains - If you rely on multiple vendors for critical services
- Companies handling sensitive data - When vendors have access to customer information, financial data, or intellectual property
- Regulated industries - Where compliance frameworks explicitly require vendor risk management
- MSPs and service providers - Who need to assess both their own security and their clients' vendor risks
- Anyone seeking cyber insurance - Insurers increasingly require documented third-party risk programs
How It Works in Practice
Let's walk through a realistic scenario:
You're onboarding a new cloud software vendor that will have access to customer contact information. In your RateYourCyber dashboard, you create an assessment link and select "Sophisticated" questionnaire depth since they'll handle customer data.
The vendor receives the assessment link. With AI assistance, they complete it in about 45 minutes. The system automatically scores their responses and generates a risk report.
Results show they score 68% overall - below your 75% threshold for vendors with customer data access. Specific gaps are identified: no incident response plan documented, inconsistent patch management, and backup testing that happens only annually.
The platform generates a remediation roadmap for the vendor and suggests contract clauses requiring these specific issues to be addressed within 90 days. You include these in your vendor agreement.
Three months later, the vendor completes a follow-up assessment showing the gaps have been remediated. Their score improves to 79%. You have documented evidence of due diligence and improvement for both regulators and insurers.
Continuous Assessment, Not Annual Audits
The key difference is continuity. Instead of annual snapshots that immediately become outdated, you maintain ongoing visibility into vendor risk.
When vendors remediate issues, their scores update. When new vulnerabilities emerge, you know immediately which vendors are affected. When regulators ask about your third-party risk program, you have current data, not year-old questionnaires.
Integration with Your Security Program
Third-party risk assessment doesn't exist in isolation. In RateYourCyber, vendor assessments integrate with your own security posture.
Your Vendor Management domain score reflects how systematically you assess and monitor suppliers. Gaps in vendor security feed into your overall risk picture. Remediation timelines appear in your security roadmap alongside internal improvements.
This creates a complete view: your security posture plus your supply chain risk, all in one place.
Start Assessing Third-Party Risk Today
See how RateYourCyber transforms vendor security assessment from annual compliance exercise into continuous risk management.
What you get:
- Flexible questionnaire depths (20, 80+, or 150+ questions) based on vendor risk
- AI-assisted completion that speeds up assessments and improves accuracy
- Automatic risk scoring against industry benchmarks
- Tailored remediation roadmaps with specific timelines
- Real-time dashboards showing your supply chain risk
- Contract clauses generated from actual security gaps
This is third-party risk management designed for the modern threat landscape.
Start Your Assessment Learn More