Most policy libraries hand you a Word document full of placeholder text and call it a day. Then you spend weeks guessing what actually applies, filling gaps, and hoping it holds up in an audit.
We took a different route.
How it works
Complete your assessments on RateYourCyber across cybersecurity, business continuity, data privacy, AI security, HR, and physical security. The platform already understands your organisation, industry, size, jurisdiction, and risk profile.
Choose a policy. Set your frameworks, your business and governance goals, and specific requirements. The platform generates a policy aligned to where you are now and where you need to be.
Not generic. Not theoretical. Yours.
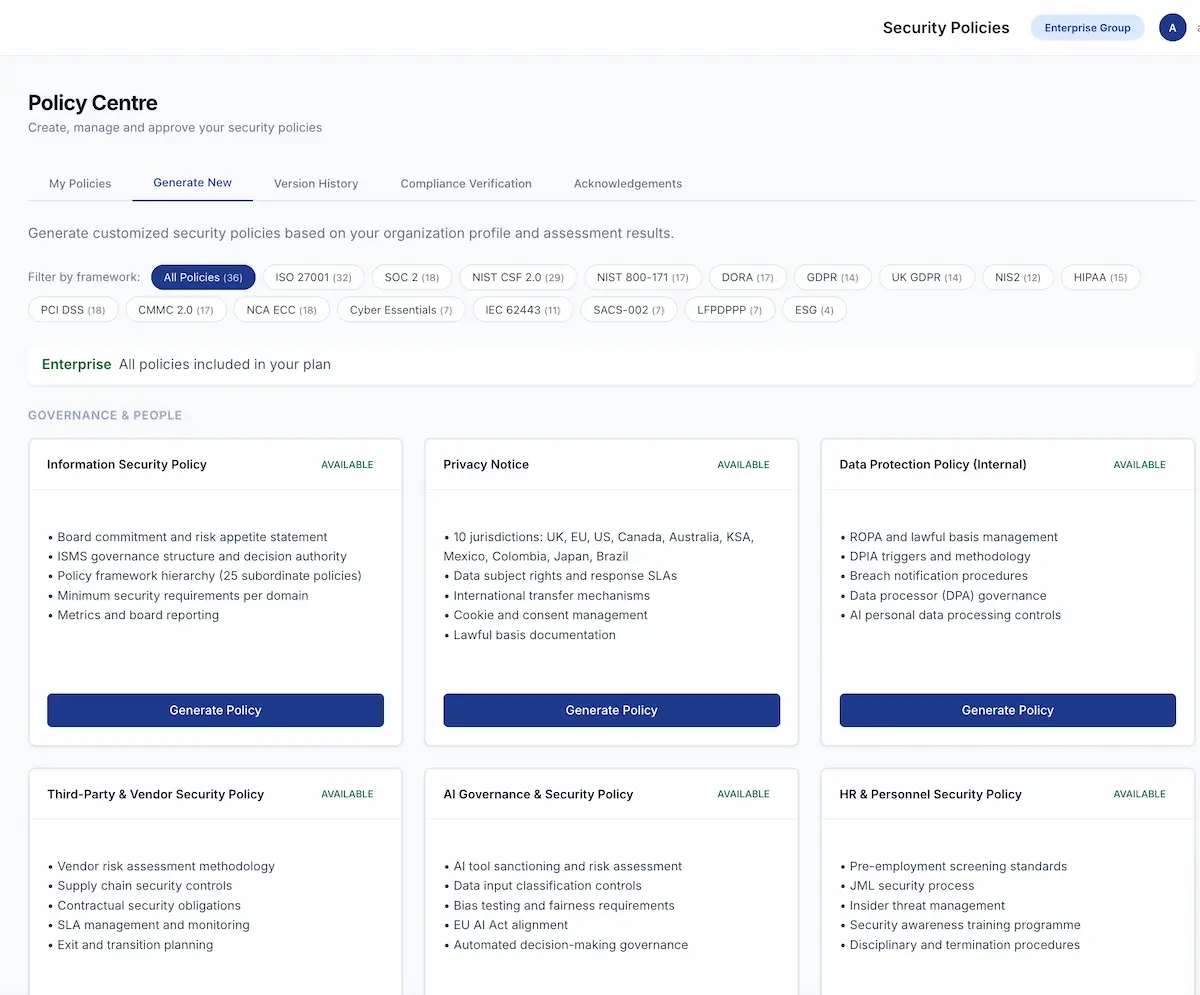
Three maturity tiers across 17 frameworks
Every policy is available at three maturity levels: Basic, Developing, and Advanced. Each tier is mapped to the frameworks you care about and connected to the tools you already use.
36 policies covering ISO 27001, SOC 2, GDPR, DORA, NIS2, PCI DSS, HIPAA, NCA ECC, CMMC, NIST CSF, EU AI Act, Cyber Essentials, and more. From Information Security and Incident Response to AI Governance, ICS/OT Security, Data Loss Prevention, and Wireless Security.
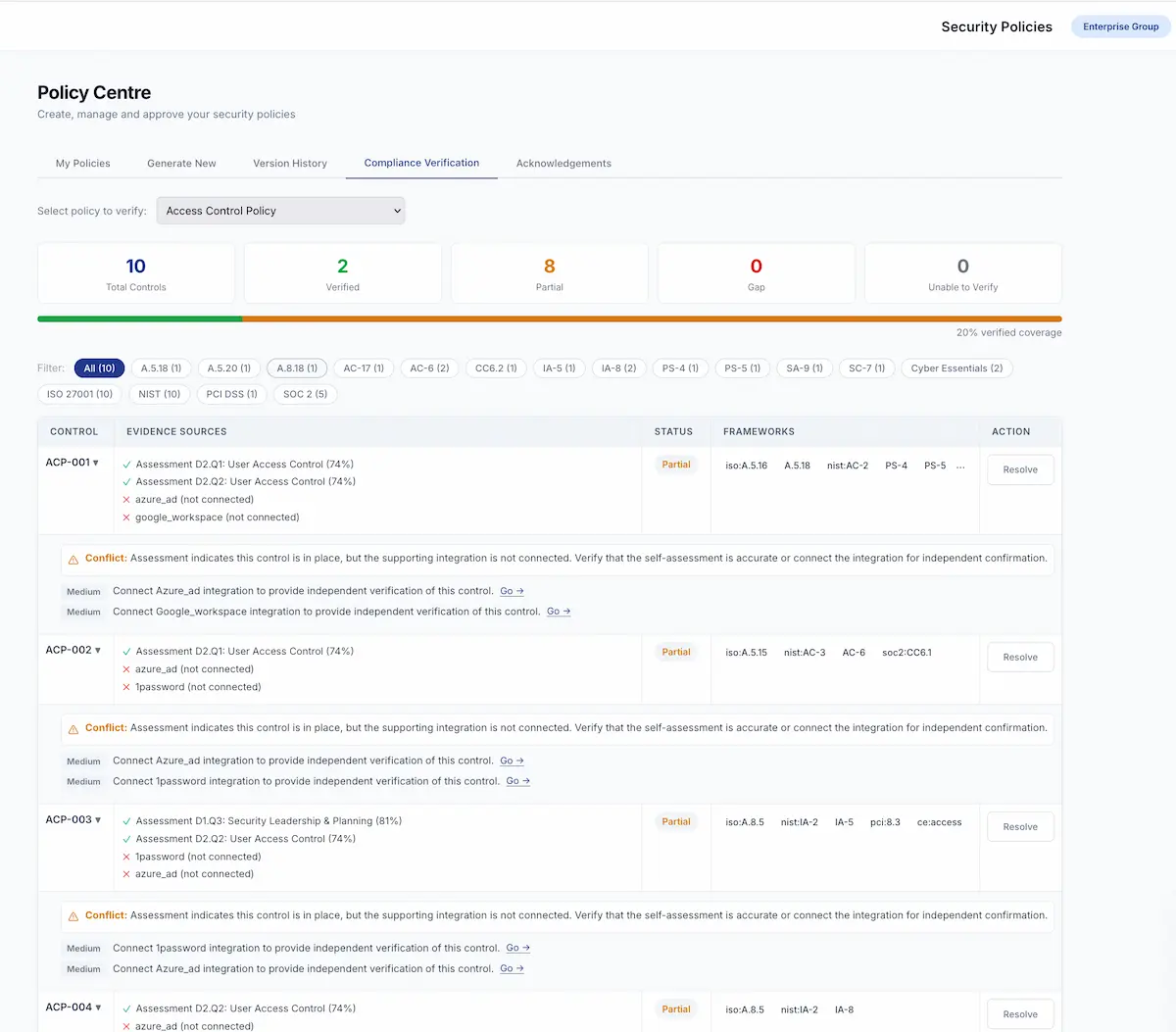
Compliance verification, built in
Every policy maps controls against real evidence from your assessments, scans, and integrations like Cloudflare, CrowdStrike, SentinelOne, 1Password, Jira, Snyk, Intune, and Google Workspace.
You can see what is fully verified, what is partially covered, and where the gaps are. If something does not line up, it is flagged with guidance on how to fix it.
Filter by framework. Drill into detail. Stay audit-ready.
Full lifecycle management
Policies move through a proper lifecycle: Draft, Approval, and Approved. Version control and supersession tracking are built in, so you always know which version is current and what changed.
Staff acknowledgements are captured with name, role, and timestamp. Everything syncs automatically to your ISMS evidence library.
No more files buried in shared drives with five versions of the same document. One source of truth, always current, always auditable.
Connected to everything else
Policies do not sit in isolation. They connect to your risk register, your compliance mappings, your evidence library, and your assessment results. When your posture changes, you can see which policies need attention.
That is the difference between a policy library and a policy programme.
See Your Policies
Generate policies from your actual assessment data, not templates.
Start Your Assessment Get in Touch